Entering Disobey 2024
In 2024 I participated Disobey for the second time. I hadn’t planned to participate back then but on the eve of the event, I started regretting this decision a lot. Loads of exciting stuff and presentations would be there, in addition to so many interesting people.
That’s when I noticed there was still one ticket available through the Unauthorized access challenge, for whoever could sneak in first and find NotMyNick.

I remembered from last year’s event a less supervised part of the event area. Additionally, I found photos of that year’s access card and wristband. With the help of standard MacOS software, an access card printer, a regular printer, and some technical and moral support from a few colleagues, I crafted myself a fake card and a paper wristband.
The entry challenge started at 11.30, and about ten minutes later I was shaking hands with NotMyNick to mark the end of the challenge.
Could I repeat it in 2025?
In his closing speech of Disobey 2024 NotMyNick announced that in 2025 the competition would be extended so that it would be possible to social engineer NotMyNick to give away one ticket in 2025. That was the starting point when I started thinking whether I could come up with a feasible plan to social engineer him the next year.
Having organised events for many years in the past I remembered that without exception the start of the event would always be stressful, hectic and no matter how well you’d have prepared, there were always last minute changes or things that weren’t done for one reason or another. In best cases the event participants know nothing about all that, but often someone is missing their badge or information about last minute changes hasn’t reached the registration desk. The most awkward situations were the ones when a speaker was missing their badge.
Based on my previous experiences with events, I assumed that I would have a good chance to get to speak with NotMyNick in a situation where I would be a speaker of the event but the event personnel couldn’t find my name, ticket, or anything else from their lists. But how would that happen?
Inviting myself to speak at Disobey
I figured that the plan of becoming a speaker and having any chance of it to work, would need to include a mix of last minute timing, credible enough evidence and a circumstance that would impede NotMyNick to immediately blow my plan, say, through a walkie talkie without me even getting the chance to get too see him.
Timing
As the event and its speakers are decided weeks before the event through a CFP, I thought that the only slight chance to have my plan work would be to get invited as close to the event as possible and because of some unexpected changes at the organiser’s end. Because of the timing and unexpectedness, email would be used for communicating with me and the organiser.
Evidence
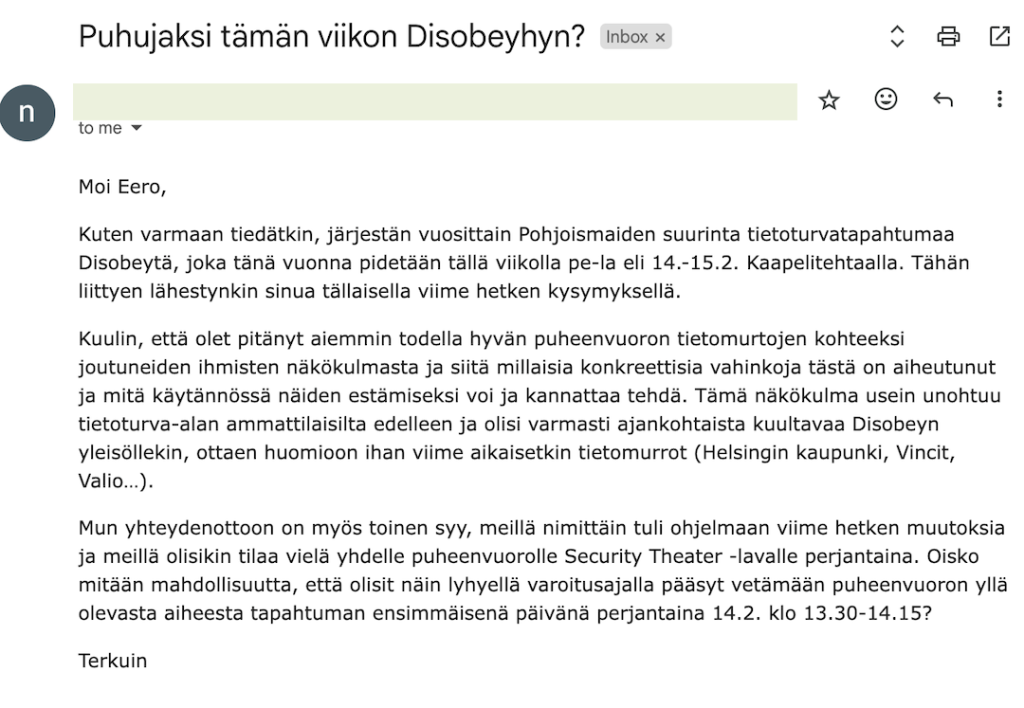
In order for me to be considered a real speaker I reasoned that I would have to be able to show some evidence. An email conversation with me and NotMyNick was the most obvious and easiest form of evidence I came up with.
As I don’t know how to spoof email addresses and I didn’t plan to start learning it, I thought that I don’t actually even have to spoof anything, as my plan was to have the email conversation between me and myself. It was enough to have an email address of which display name I would change as NotMyNick’s email address.
Forging an email conversation is so easy that I didn’t consider it to suffice for getting into a security event. Having myself listed as a speaker on Disobey’s website should be enough convicing a piece of proof that my claims could be considered to be true. Since hacking Disobey’s website was obviously out of the question, I thought that setting up a clone website on a similar domain would do the trick. After thinking of various options, I found out it’s possible to have a .fi domain with a special d, namely đ, which seemed to be exactly what I needed.
Finally, I came up with fake name and created myself a security professional’s profile and summary of “my presentation” with the kind help of Copilot.
Circumstance
As for the circumstance, it should be such that the event personnel couldn’t quickly contact NotMyNick to check whether my claims are true or not. So I planned, that I would have to agree with him, that I would join the event at the very moment NotMyNick would be on stage giving his opening speech and we would also agree to meet with him at the backstage around 12.45 as my presentation would start already at 13.30. This was agreed in the email conversation between me and “NotMyNick” (also me).
How to actually execute the plan?
So I now had a website and email conversation telling my alter ego would be speaking at Disobey 2025 and my plan was to join the event on the first day at 12.30. How did I plan to actually get in?
Best case scenario
I assumed that showing up at the doors and telling the personnel that NotMyNick had left my bracelet at the info desk would get me there. If not, I would have the email conversation as evidence.
If I’d get to the info desk where there obviously wouldn’t be a bracelet waiting for me, the event personnel should believe me and my evidence. Then they would fetch a bracelet for me and then take me to the back stage to meet NotMyNick, as agreed with him.
Once getting in contact with NotMyNick, I’d present myself and tell him that I’m there as agreed and we should proceed to go through the details of my presentation. By then, NotMyNick would most likely be very puzzled and start asking what is this all about. I’d refer to my evidence and sooner or later I will have to face the fact that I haven’t actually been invited as a speaker. That’s when it’s my turn to become puzzled.
The bottom line is, I have cancelled my business trip to a client up north, planned a presentation on a very tight schedule, invited my clients to come and listen to my presentation and agreed to meet them afterwards at the event. Is this a bad joke or has NotMyNick’s email been compromised? What about the website? This is a total humiliation!
If I play my part well, NotMyNick will believe me and out of pity let me stay at the event, or get my bracelet in case I didn’t get one already. At that point I would also let NotMyNick know, that I managed to social engineer a ticket from him. In a less optimal scenario he won’t believe a single word I’m saying, laugh and tell me to get the h*ll out of there. At which point I hope I’d still be the first one to meet him without a proper bracelet and thus be eligible to have one as a reward.
Plan B
The best case scenario contains so many variables of which result may lead me to be removed from the venue without getting the chance to meet NotMyNick, that I felt I must have a plan B.
The most probable risk is, that the event personnel will notice that my evidence is fake. In that case my plan is to start playing a victim. Someone for some very nasty reason has chosen to make me look like a fool, making me to cancel my business trip up north and so forth. In this case, I will have to both convince the event personnel, and instead of getting escorted out immediately, have them ask NotMyNick to get there to try to make sense of what’s going on. In this case I still believe there would be a good chance to get a bracelet from NotMyNick, after which I could end the show and let him know that he has been social engineered.
I also imagine that someone might want to see other proof of who I claim to be. For this, I’ve made a fake company badge with my picture and fake name, hoping it to be enough. As a part of my story, I will also tell them that for obvious reasons I don’t carry proper ID or payment cards in such an event.
Worst case scenario
The worst case scenario is that I won’t be let in at the info desk nor they will ask NotMyNick to come to figure out what’s going on. Or I will be escorted out from the info desk once it turns out there isn’t a bracelet waiting for me.
In this case I’m still left with the chance to try to sneak in through a less guarded door, that could be somewhere around the venue, and given that no one else yet had sneaked in and got a ticket from NotMyNick.
Even if that won’t work, the worst and most obvious end result is, that I won’t get in and miss a certainly great event 🙁
Why bother?
If you read this far, you might wonder why bother in the first place and not just buy a ticket just like everyone else does (excl. hacker puzzle solvers)?
As it obvious by now, I’m not a technical expert so I would basically never have the chance to win a ticket through the hacker puzzle. Still, I’m interested in learning about cyber security from the less technical side and especially understand what kind of human behaviour can lead to major negative consequences. For learning about this the Unauthorized Access Competition is excellent. If I manage to convince the event personnel and NotMyNick to give me a ticket, I think it’s fair for assume that eventually anyone can be fooled. In addition, I learned so many new fascinating things along this process!
So how did it go?
When writing this, I still don’t know. I will write it here once I know what happened. Whether I will even publish this piece of depends on whether I’ll reach NotMyNick and if also he is OK with me publishing all this.
UPDATE 14.2.2025:
Everything went more or less according to the plan 👏🏻
Amazing event ahead!


DISCLAIMER: I’m aware that the site is unfortunately poorly accessible and it’s best viewed on a mobile device screen.